GCP Security & Cloud Optimisation Experts.
We help GCP teams harden their cloud posture, eliminate waste, and ship infrastructure as code — through hands-on consulting engagements and a SaaS platform built from the same playbook.

Critical risks mapped
Monthly savings identified
Terraform templates
Median draft time
Built on deep GCP expertise
Consulting services
HANDS-ON GCP
ENGINEERING EXPERTISE.
CloudXero began as a GCP consulting practice. Every service we offer is grounded in real infrastructure work — architecture reviews, security audits, FinOps engagements, and Terraform IaC delivery. The SaaS platform is the productised version of that playbook.
IAM, firewall, SCC posture reviews
Spend analysis + rightsizing plans
Landing zones, VPC, org design
Module delivery + CI/CD pipelines
Recent engagement outcomes
Identified $18k/month in idle compute, oversized GKE pools, and detached disks for a Series B fintech — delivered in 6 weeks.
Scoped audit surfaced a lateral movement risk spanning 4 production projects. Terraform remediation merged within 48 hours.
Delivered a private GKE cluster, Shared VPC, and Workload Identity setup with full Terraform modules for a healthcare SaaS team.
Our story
BUILT BY ENGINEERS
WHO LIVE IN GCP.
CloudXero was founded by GCP engineers who spent years inside complex, high-stakes cloud environments — hardening IAM policies under pressure, cutting six-figure monthly bills, and shipping Terraform modules that actually make it to production.
We got tired of watching teams repeat the same mistakes: overprivileged service accounts, idle compute nobody noticed, and security findings that sat in a spreadsheet for months. So we built the tooling we always wished existed — and then turned it into a consulting practice that uses the same playbook on every engagement.
Every CloudXero engagement ships working code. Every platform finding comes with a Terraform fix. We don’t do slide decks without substance.
Google Cloud Certified
Professional Cloud Architect · Professional Cloud Security Engineer
Security-first mindset
Every engagement starts with IAM, SCC, and network posture — before anything else.
FinOps Certified
FinOps Foundation practitioner. We tie every recommendation to a dollar figure.
Code, not decks
Engagements close with Terraform modules, not PowerPoint. Handover is a git repo.
Platform capabilities
DETECT. EXPLAIN. CODIFY.
Security visibility, SecOps context, FinOps prioritization, and Terraform output in a single operator workflow — not split across four tools.
Security Visibility
Surface exposed services, IAM risk, and cloud posture drift before issues turn into incidents.
12 critical risks detected
FinOps Optimization
Find idle spend, rightsizing opportunities, and cost anomalies with enough workload context to act safely.
$18.4k recoverable per month
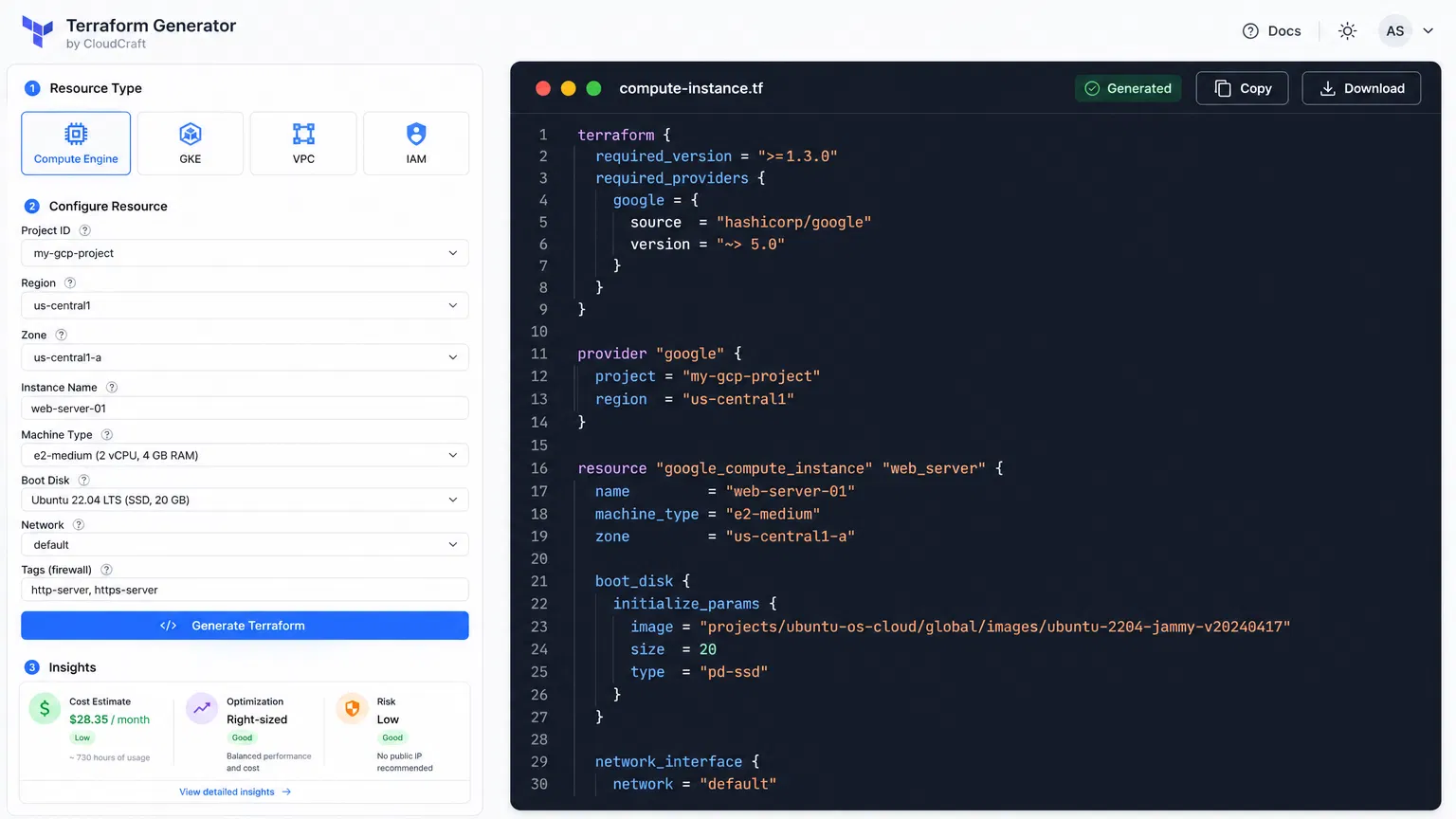
Terraform Automation
Turn findings and architecture recommendations into review-ready Terraform without losing engineering control.
128 templates · 18 sec drafts
Blog → Terraform Flywheel
EVERY POST SHIPS WITH CODE.
CloudXero publishes GCP best-practice guides twice a week. Every article automatically generates a production-ready Terraform module so you can go from reading to deploying in minutes.
Blog Published
A new GCP best-practice article goes live on cloudxero.net — IAM, GKE, VPC, SecOps, FinOps.
Pattern Extracted
CloudXero reads the article and identifies the GCP resources, security controls, and architecture patterns described.
Terraform Generated
A parameterised, production-ready Terraform module is generated — main.tf, variables.tf, outputs.tf, README.
CI/CD Pipeline
Free: download & copy. Pro: push to GitHub PR. Team: full pipeline with plan, scan, cost estimate, and apply.
How it works
FROM RISK TO FIX IN ONE FLOW.
Detect GCP Risk
Scans IAM bindings, firewall rules, SCC findings, and resource posture across connected projects.
12 critical risksCorrelate SecOps
Findings are matched against Chronicle UDM events so you can see which risks already triggered alerts.
3 Chronicle alertsEstimate Cost Impact
Each finding is priced so idle compute, oversized clusters, and unused storage surface as dollar values.
$18.4k savingsGenerate Terraform Fix
CloudXero drafts review-ready HCL for the highest-priority findings so engineers review instead of rebuild.
<20 sec draftTerraform Hub
CLOSE THE LOOP
WITH CODIFIED FIXES.
CloudXero drafts Terraform around recommendations, architecture patterns, and safer defaults so teams move faster from insight to change — without rebuilding the same fix by hand.
Expert services
ENGINEERS, NOT VENDORS.
Every engagement produces working infrastructure, real documentation, and outcomes you can measure.
GCP Infrastructure Architecture
Design resilient project structures, networking, IAM, and deployment patterns that scale cleanly.
Cloud Security & Compliance
Expose misconfigurations, risky access paths, and cloud control gaps before they become audit problems.
SecOps / Chronicle SIEM
Build detection coverage, log pipelines, and Chronicle workflows that reduce investigation time.
FinOps Optimization
Cut recurring waste across compute, storage, and analytics without destabilizing production workloads.
Secure Landing Zones
Establish guardrailed foundations for new environments with networking, identity, logging, and policy baked in.
Terraform / IaC Automation
Move from architecture guidance to reusable Terraform modules your team can review and ship quickly.
What teams say
TRUSTED BY PLATFORM TEAMS.
"CloudXero surfaced a firewall and IAM path we had missed, then drafted the Terraform changes our team merged the same week."
Priya S.
Head of Platform, retail SaaS
"The FinOps view gave us a clean map of idle services and rightsizing wins. We cut recurring spend without flying blind."
Marcus T.
Cloud Operations Lead, data startup
"It feels like a lighter, more actionable control plane for GCP teams that still want direct access to expert architecture help."
Elena R.
CISO, enterprise healthcare
Pricing
CLEAR PRICING.
REAL VALUE.
Starter
For teams validating the product motion on a single project.
CloudXero Platform · No card required
Pro
For platform teams that need actionable insights and fast Terraform handoff.
CloudXero Platform · Cancel anytime
Enterprise
For multi-org environments and regulated cloud programs.
Consulting engagement · Custom scope
FAQ